A new exploit has been found that targets SSLv3 named “POODLE”, which stands for Padding Oracle On Downgraded Legacy Encryption. It’s an exploit that has been found by google. More about it and its impact can be read here: http://googleonlinesecurity.blogspot.com/2014/10/this-poodle-bites-exploiting-ssl-30.html . If you are on a shared or reseller account, you have nothing to worry about. If you are currently on a VPS or dedicated server, we ask that you please do the following to protect your server and/or submit a ticket so we can do them for you.
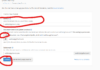
1: Login to your WHM panel as the root user. On the primary login screen, click on “service configuration”.


3: Now, click on Include Editor

Finally, under the section “Pre Main Include”, select the ‘all versions’ option which will load an empty box that allows you to type into. In this box, type in:
SSLHonorCipherOrder On
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2

Then click on update. This will save your changes. Now, restart apache so the new changes take place. You have now successfully disabled SSLv3 on a cPanel/WHM server or VPS running on Centos 6.X (If you are a wen host python customer, you are most likely using CentOS 6.X)